How to logout a user in Angular
Proper user logout requires clearing authentication tokens, resetting application state, and redirecting to the login page. As the creator of CoreUI with 12 years of Angular development experience, I’ve implemented logout functionality for enterprise applications with strict security requirements.
The most secure approach combines token removal, state cleanup, and navigation in a single logout service method.
How to sanitize inputs in Node.js
Input sanitization removes or encodes potentially dangerous characters from user input to prevent security vulnerabilities like XSS, SQL injection, and command injection. As the creator of CoreUI with 12 years of Node.js development experience, I’ve secured applications serving millions of users by implementing proper input sanitization strategies that block malicious payloads while preserving legitimate user data.
The most reliable approach combines validation libraries with context-specific sanitization.
How to refresh JWT tokens in Angular
Automatic JWT token refresh prevents users from being logged out during active sessions while maintaining security. As the creator of CoreUI with 12 years of Angular development experience, I’ve implemented token refresh mechanisms for enterprise applications with millions of authenticated users.
The most secure approach is to use an HTTP interceptor that detects 401 errors and refreshes the token automatically before retrying the failed request.
How to store tokens securely in Angular
Storing authentication tokens securely is critical for preventing XSS attacks and unauthorized access. As the creator of CoreUI with 12 years of Angular development experience, I’ve implemented token storage strategies for enterprise applications handling sensitive financial and healthcare data.
The most secure approach is to use httpOnly cookies for storage and avoid localStorage entirely for sensitive tokens.
How to implement role-based auth in Angular
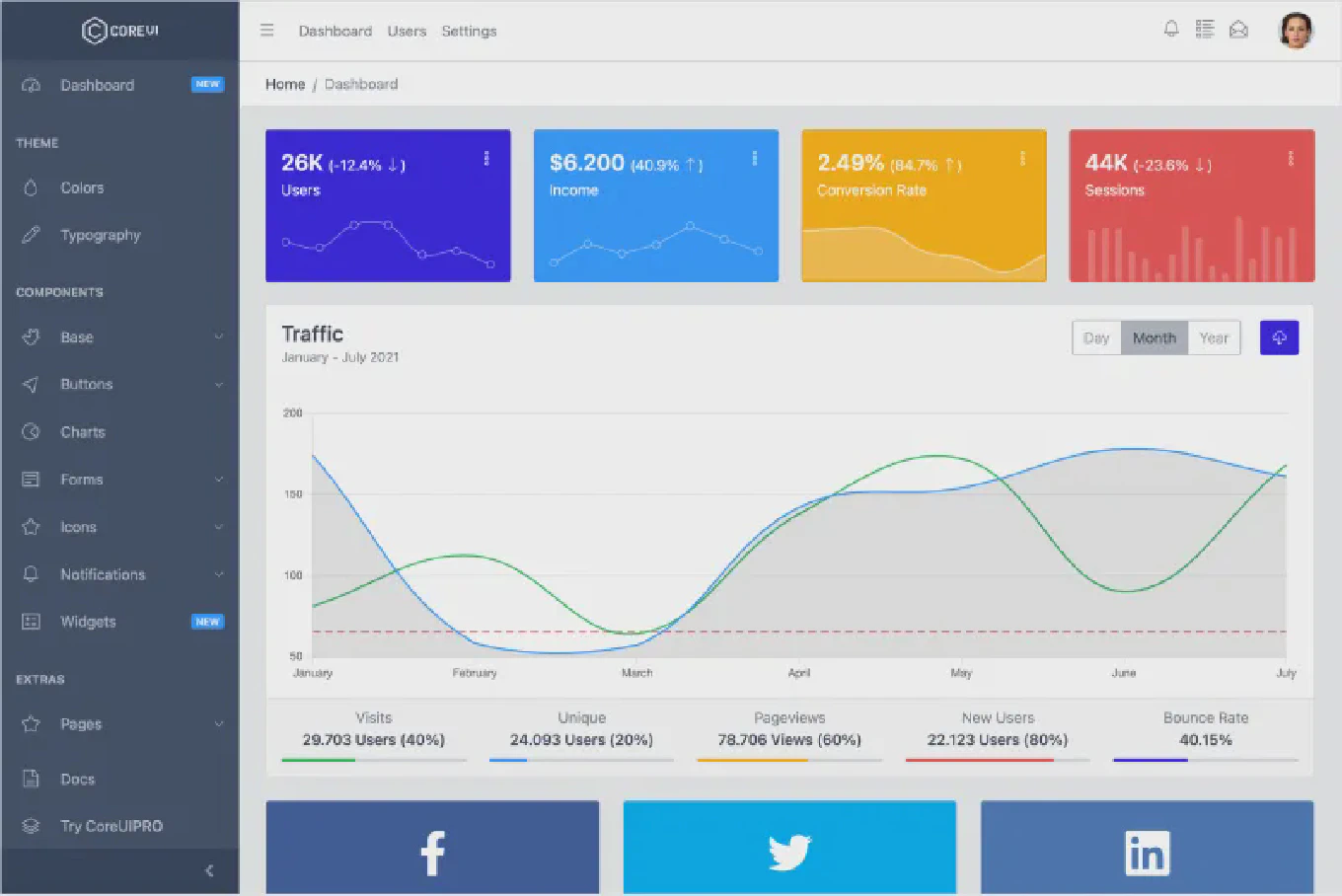
Role-based authentication (RBAC) allows you to control access to routes and features based on user roles. As the creator of CoreUI, I’ve implemented enterprise-grade authentication systems for Angular applications serving millions of users.
The most maintainable approach combines an auth service, route guards, and structural directives to enforce role-based access control throughout your application.
How to implement JWT authentication in Angular
JWT authentication provides stateless, secure authentication using JSON Web Tokens for API authorization, enabling scalable authentication across distributed systems. As the creator of CoreUI, a widely used open-source UI library, I’ve implemented JWT authentication in Angular applications throughout my 12 years of frontend development since 2014. The most robust approach is using HTTP interceptors to automatically attach JWT tokens to requests and handle token refresh for expired tokens. This method centralizes token management, provides automatic authorization headers, and implements seamless token renewal without user intervention.
How to implement authentication in Angular
Authentication provides secure user access control, protecting routes and resources from unauthorized users while managing login sessions and tokens. As the creator of CoreUI, a widely used open-source UI library, I’ve implemented authentication systems in enterprise Angular applications throughout my 12 years of frontend development since 2014. The most effective approach is creating an authentication service with route guards to protect routes and HTTP interceptors for token management. This method centralizes authentication logic, provides reusable guards, and automatically handles token injection for API requests.
How to enable GPG signing in Git
Enabling GPG signing for Git commits ensures commit authenticity and maintains security in collaborative projects and open-source repositories. As the creator of CoreUI, a widely used open-source UI library, I’ve enforced commit signing in production repositories throughout my 25 years of development experience. The most straightforward approach is configuring Git to automatically sign all commits with your GPG key. This method provides cryptographic proof of authorship for every commit you make.
How to verify signed commits in Git
Verifying signed commits ensures the authenticity of code contributions and maintains security in collaborative projects.
As the creator of CoreUI, a widely used open-source UI library, I’ve enforced commit signing in enterprise repositories throughout my 25 years of development experience.
The most straightforward method is using git log --show-signature to display GPG signature verification status for each commit.
This approach provides clear indication of whether commits are properly signed and verified.
How to sign commits in Git
Signing Git commits with GPG keys verifies commit authenticity and proves that commits actually came from you. As the creator of CoreUI with over 25 years of development experience, I’ve implemented commit signing for security-critical enterprise projects. The most effective solution is to generate a GPG key, configure Git to use it, and enable automatic commit signing. This approach provides cryptographic proof of commit authorship with verified badges on hosting platforms.