How to create a route guard in Angular
Securing application routes and managing navigation access is a fundamental requirement for any professional web application.
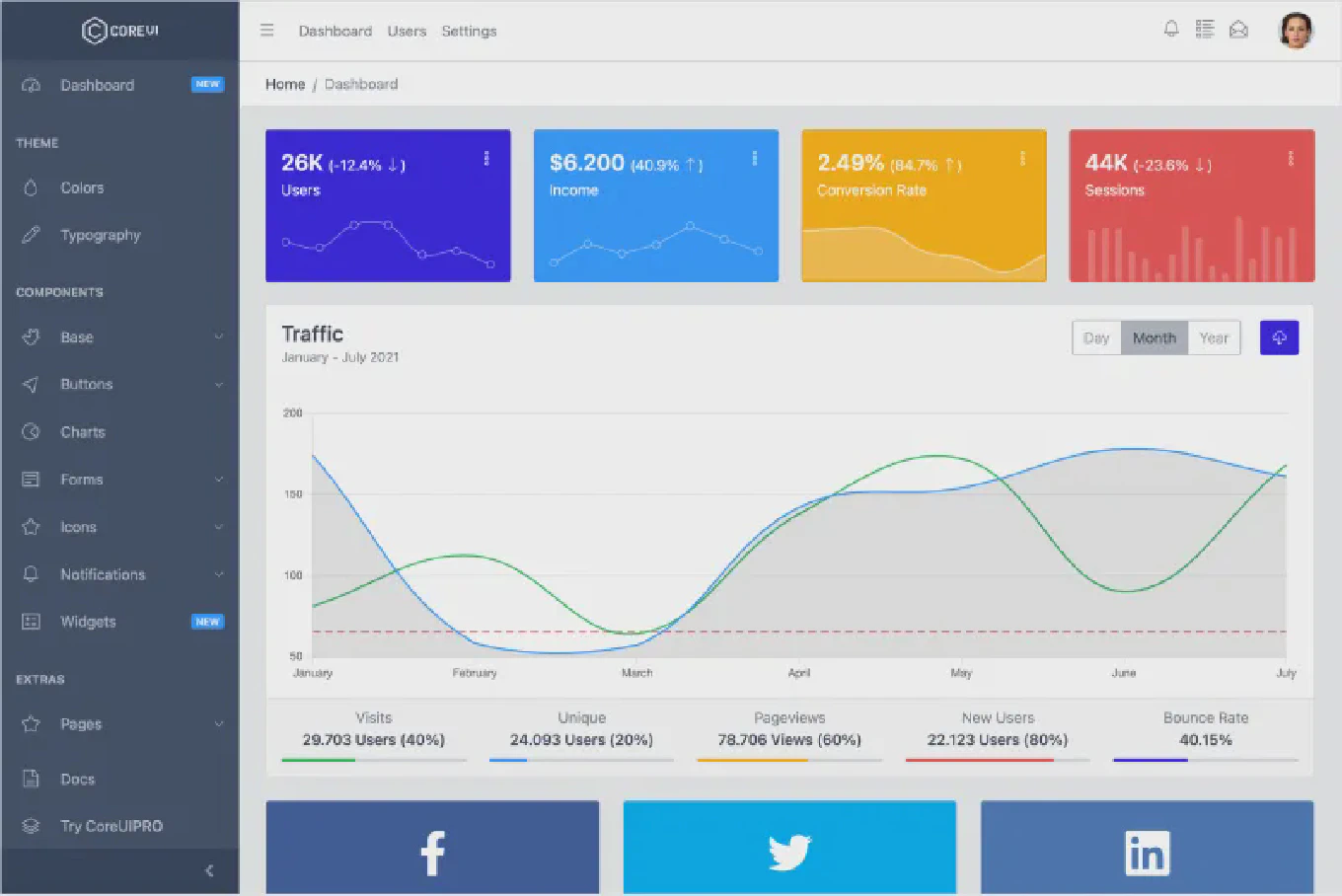
With over 25 years of experience in software development and as the creator of CoreUI, I have built and secured hundreds of complex Angular architectures.
From my expertise, the most efficient and modern way to handle this in Angular is by using Functional Route Guards, which were introduced to replace the older, more verbose class-based approach.
This modern pattern leverages the inject function to create lightweight, modular, and highly testable security checks for your routes.
How to consume private npm packages in React
Managing dependencies in a professional React environment often requires access to proprietary code stored in private registries.
With over 25 years of experience in software development and as the creator of CoreUI, I have architected numerous internal design systems that rely on private npm packages for secure distribution.
The most efficient and modern solution for consuming these packages is to configure a project-level .npmrc file that utilizes environment variables for authentication tokens.
This approach ensures that your credentials remain secure while allowing your React application to build seamlessly across local environments and CI/CD pipelines.
How to implement password reset in Node.js
Password reset requires generating a time-limited secure token, sending it to the user’s email, and allowing the user to set a new password only when they provide the valid unexpired token. As the creator of CoreUI with 25 years of backend development experience, I implement password reset in every authentication system I build, and the most important security principle is that the token is single-use and expires quickly. The flow has two endpoints: one to request the reset (generates and emails the token) and one to confirm the reset (validates the token and sets the new password). Both endpoints must return generic success messages to prevent email enumeration attacks.
How to implement email verification in Node.js
Email verification confirms that a user owns the email address they registered with, preventing spam accounts and ensuring communication reaches real users.
As the creator of CoreUI with 25 years of backend development experience, I implement email verification in every SaaS application I build to maintain data quality and comply with email regulations.
The secure pattern uses a cryptographically random token stored in the database with an expiry timestamp — when the user clicks the link, you verify the token, check it hasn’t expired, and mark the email as verified.
Never use predictable tokens like user IDs or sequential numbers — always use crypto.randomBytes.
How to handle webhooks in Node.js
Webhooks are HTTP POST requests from external services notifying your application about events — a Stripe payment succeeding, a GitHub push, or a PayPal subscription renewing. As the creator of CoreUI with 25 years of backend development experience, I’ve built webhook handlers for payment processors, version control systems, and communication platforms where reliability and security are critical. The two non-negotiable requirements are: verify the webhook signature before processing, and return 200 immediately then handle the event asynchronously. Failing to verify signatures exposes you to spoofed events; slow synchronous processing risks timeouts and missed retries.
How to remove sensitive data from Git history
Accidentally committing API keys, passwords, or private certificates to a Git repository is a common security incident, and simply deleting the file in a new commit does not remove the credentials from history — they remain visible in every previous commit.
As the creator of CoreUI with 25 years of open-source development experience, I’ve dealt with this exact scenario in public repositories and the fix requires rewriting the entire repository history.
The fastest modern tool is git filter-repo, which rewrites all commits to remove the sensitive file in seconds.
Immediately rotate any exposed credentials after cleaning history — assume they have been compromised from the moment they were pushed.
How to rewrite Git history with git filter-repo
git filter-repo is the modern replacement for git filter-branch, rewriting repository history up to 50 times faster while providing a cleaner, safer interface with better defaults.
As the creator of CoreUI with 25 years of open-source development experience, I switched all projects to git filter-repo the moment it became the officially recommended tool in Git documentation.
It is not bundled with Git — install it separately — but its performance and safety features make it the clear choice for any history rewriting task.
Always work on a fresh clone before running it, as the operation cannot be undone once complete.
How to rewrite Git history with filter-branch
git filter-branch rewrites every commit in your repository’s history according to filters you define, which is necessary when you need to remove a large file, scrub sensitive data, or correct commit author information across all commits.
As the creator of CoreUI with 25 years of open-source development experience, I’ve used this tool to purge accidentally committed credentials and remove build artifacts that bloated repository size.
Note that git filter-branch is the legacy approach — git filter-repo is faster and safer for most use cases — but understanding filter-branch is still valuable for environments where installing additional tools is restricted.
Both tools permanently rewrite history and require all collaborators to re-clone or re-base after the operation.
How to hide sensitive logs in Node.js
Accidentally logging passwords, tokens, or personal data is a serious security risk that can expose sensitive information in log aggregators, monitoring tools, and stdout captures. As the creator of CoreUI with 25 years of backend development experience, I’ve seen production incidents caused by tokens appearing in plain-text logs. The safest approach is to use a structured logger like Pino or Winston with built-in redaction support that strips sensitive fields before they’re ever written. This ensures credentials never appear in logs regardless of which developer added the log statement.
How to prevent SQL injection in JavaScript
SQL injection is one of the most critical security vulnerabilities in web applications, allowing attackers to execute malicious SQL commands. As the creator of CoreUI with over 25 years of web development experience since 2000, I’ve implemented secure database access patterns in countless production applications. The fundamental defense against SQL injection is using parameterized queries and prepared statements instead of string concatenation. This ensures user input is always treated as data, never as executable SQL code.